Now Google Search is redirected in Windows 64 bit if you are infected by TDL4 rootkit
September 1 2010
 TDL rootkit infects MBR (master boot record) on the Windows 32 and 64 bit.
TDL rootkit infects MBR (master boot record) on the Windows 32 and 64 bit.
Now TDL rookit works as "bootkit". The rootkit does not infect system drivers.
It replaces the MBR of the hard drive and starts before Windows.
This allows the rookit to work on the Windows 64 bit without any problems. Unfortunately the Windows 64 bit protection could not help you to detect and remove the rootkit.
The TDL rootkit can show the "clean" MBR under normal Windows mode and fully deceive most of antiviral software.
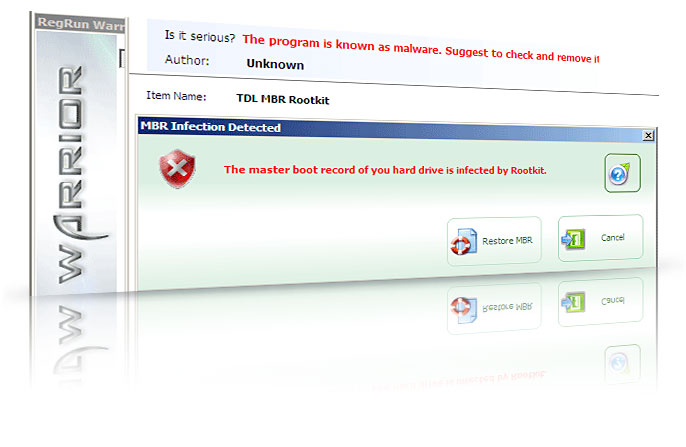
UnHackMe detects the TDL rootkit in the Windows 32 and 64 systems.
1. Check updates of the latest UnHackMe. It must be 5.99 Build 350 or higer.
It is adware/spyware/virus free.
2. Open the "Virus Scan". If you have "TDL3+Rootkit" alarm - you are infected
Get UnHackMee Warrior here
Download the Warrior CD image and burn the ISO file using any CD burning software.
More info about Warrior? Options?
3. Restart your computer to the boot CD mode.
Set the BIOS boot order.
4. If you already set up the Warrior the scan will start automatically.
Restore infected MBR. If you infected by old version of TDL - restore infected system driver from backup location.
5. Reboot to the normal Windows mode.
Look at the video lesson: TDL3++ rootkit removal.
Benefits
- Simple. No need to have special computer skills for rootkit removal.
- Quick. Rootkit removal in one reboot.
System requirements
Windows 9x, 2000/2003/XP/2008/Vista/Seven or higher 32 or 64 bit.512 Mb RAM
CD/DVD drive or USB stick.
Purchase now!
Purchase includes:
• UnHackMe Single License - Electronic Delivery
• Warrior CD Image - Electronic Delivery
People say:
LisaThis solution works great. Thanks!
Jim
Works as advertised. Keep up your good work guys!