History of the problem
History of the problem
Recently
Greatis security team tested the
W32/Almanahe.c virus.
The detailed description of the virus described can be found here:
https://www.greatis.com/appdata/d/n/nvmini.sys.htm
The virus uses the different ways of auto starting with Windows boot:
- Driver;
- Autorun.inf on the hard drive;
- File infection.
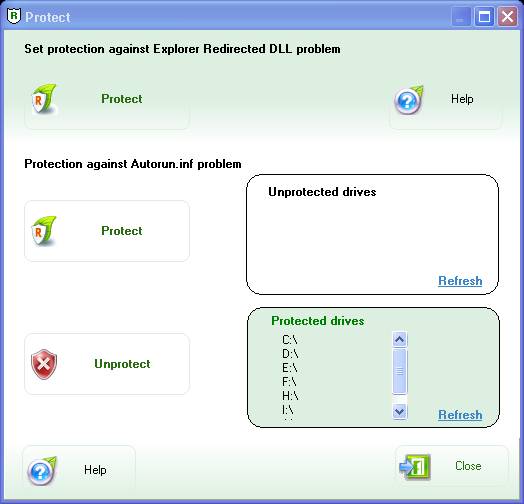
But we found that the virus uses a new
Windows startup hole, not detected by RegRun/UnHackMe.
Virus creates the file "
linkinfo.dll" and puts the file into the Windows folder.
The normal "
linkinfo.dll" was made by Microsoft is stored in the Windows\System32 folder.
Why the Windows shell "explorer.exe" loads the "linkinfo.dll" from non-standard place?
Good question!
We researched the file and registry changes made by the virus and found nothing.
After that we put the virus file "linkinfo.dll" into the Windows folder
on a clean computer and found that explorer.exe loads infected version
of the "linkinfo.dll".
We tried to copy "linkinfo.dll" from the System32 folder to the Windows folder and we see that the
Windows Explorer.exe uses "linkinfo.dll" from Windows folder again.